CISSP PRACTICE QUESTIONS – 20210125 by Wentz Wu, CISSP/ISSMP/ISSAP/ISSEP,CCSP,CSSLP,CISM,PMP,CBAPWentz Wu

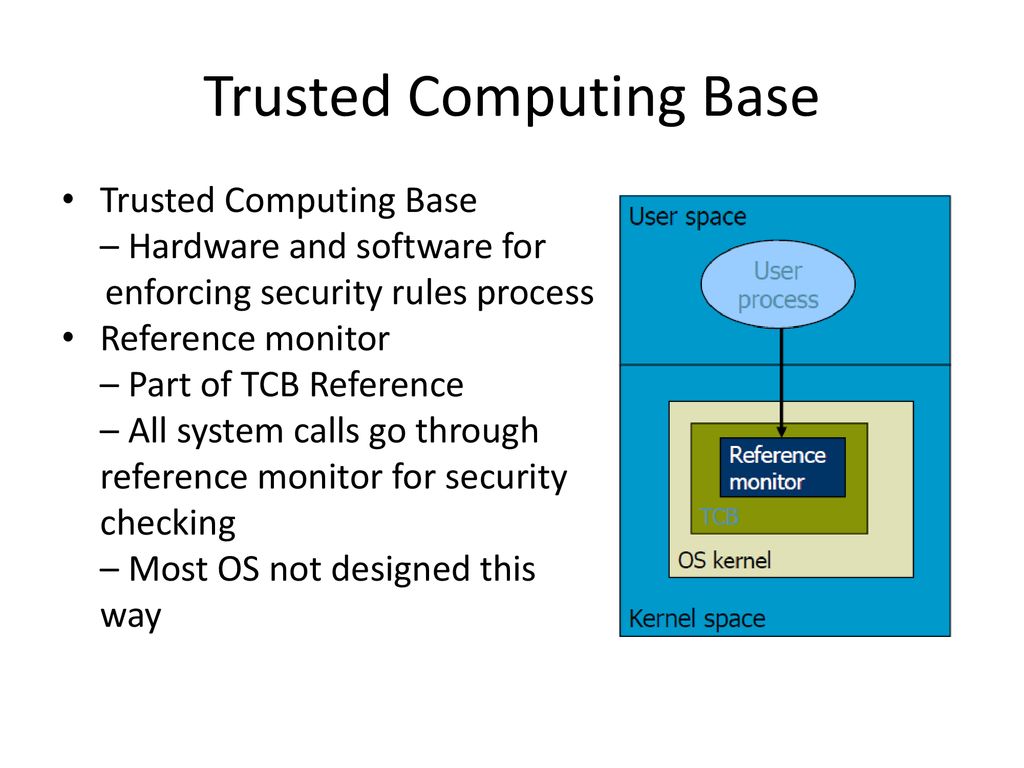
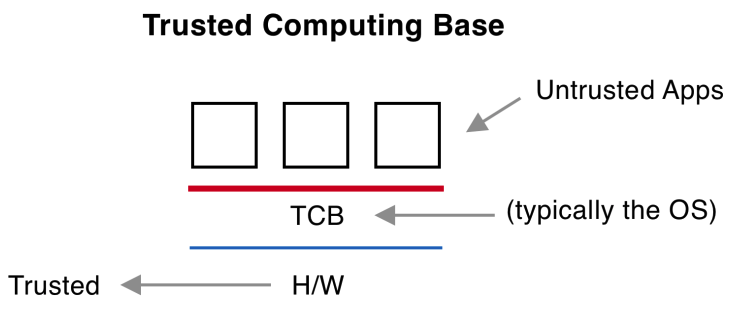
______ is the boundary that separates the trusted computing base from the remainder of the system. - Skillset

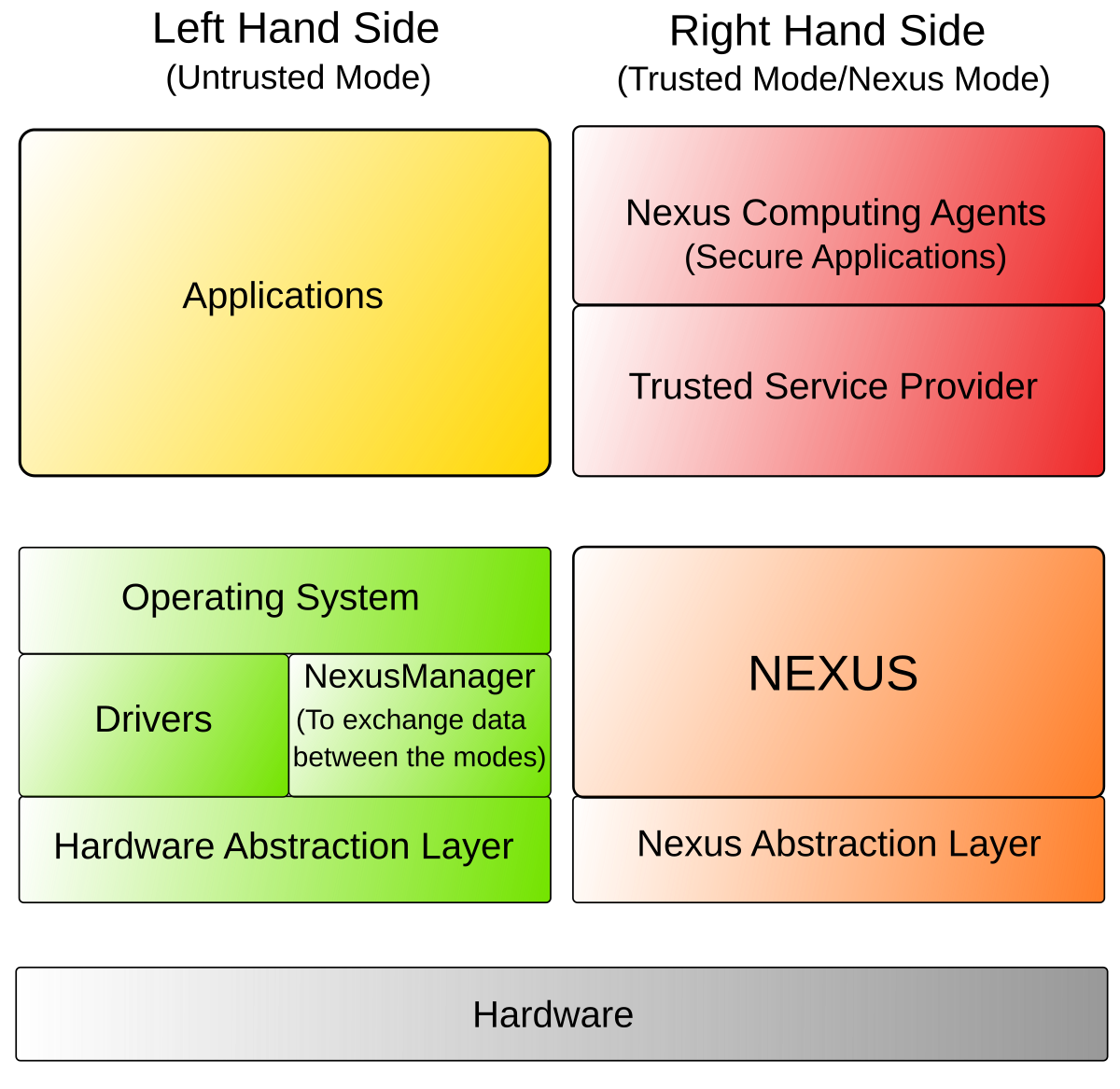
Trusted Path and Trusted Channel by Wentz Wu, CISSP/ISSMP/ISSAP/ISSEP,CCSP,CSSLP,CISM,PMP,CBAPWentz Wu

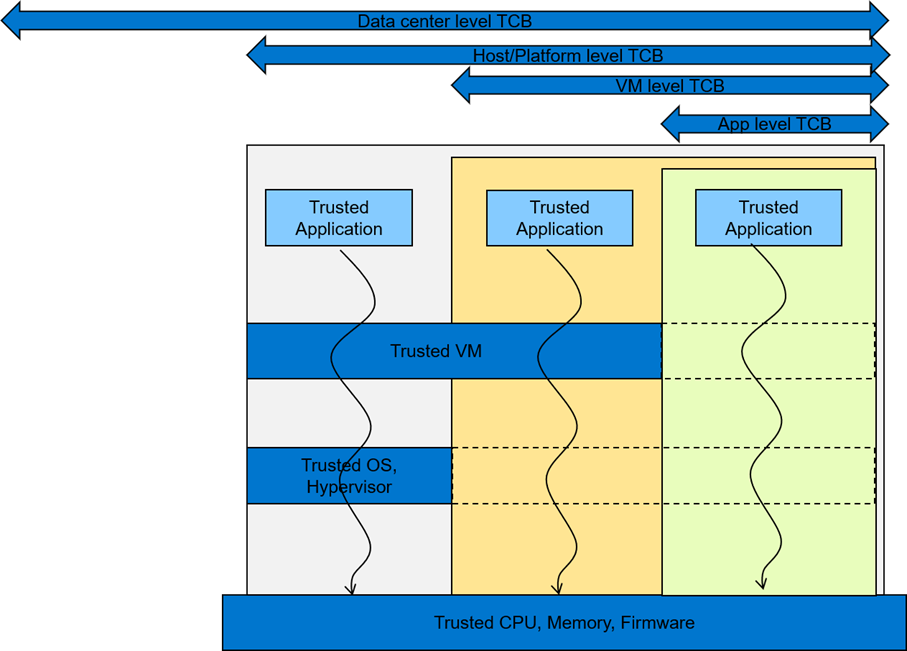
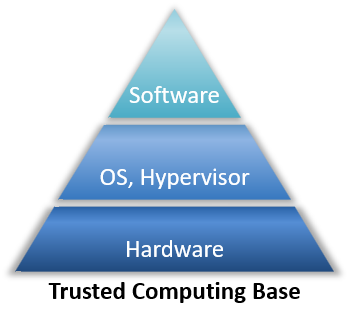
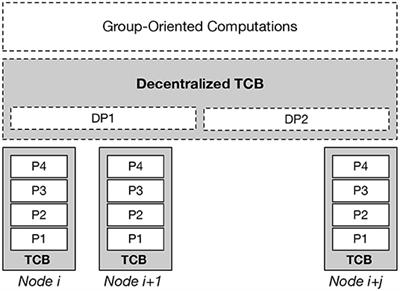
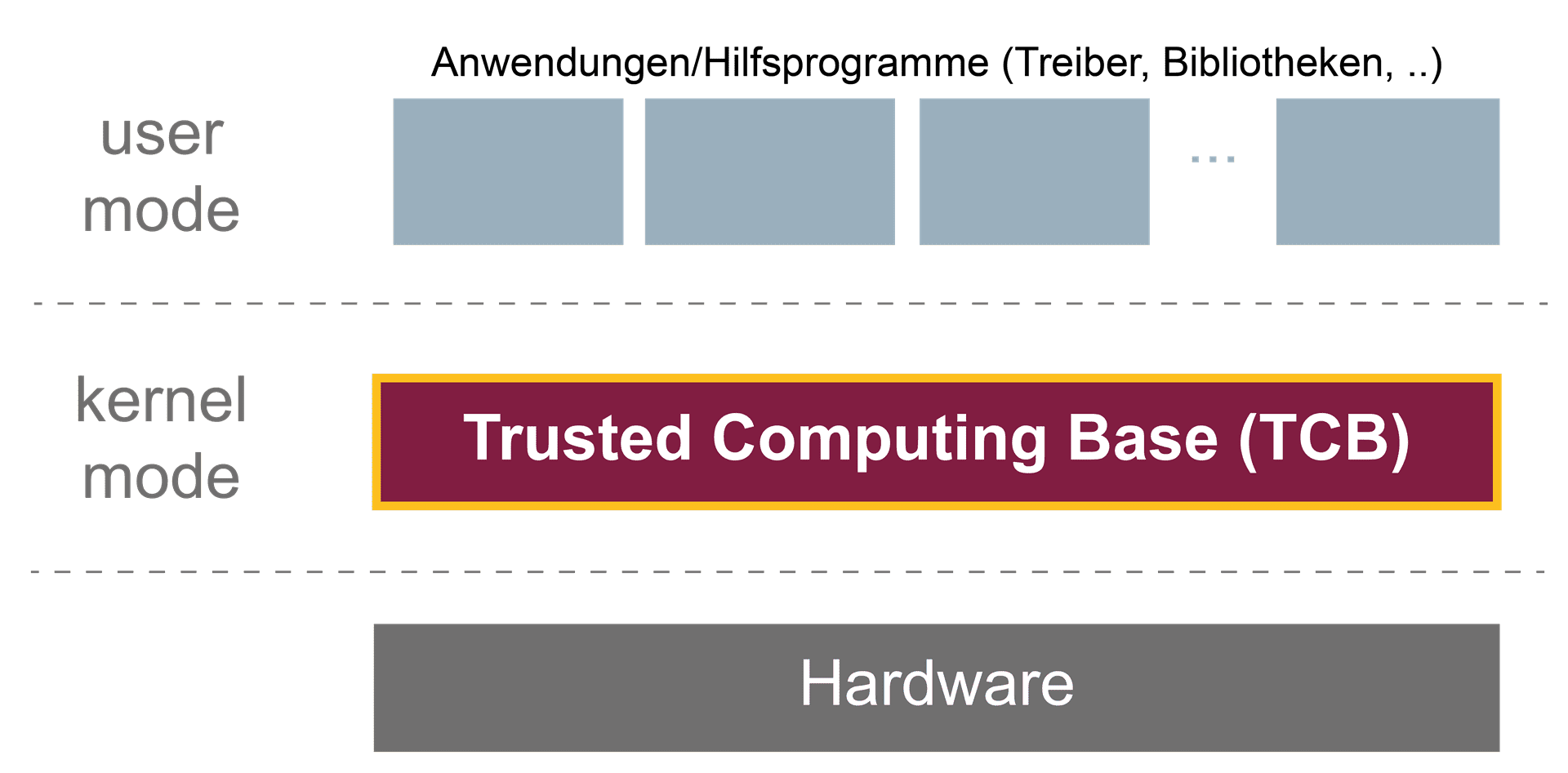
Security Architecture | CISSP Exam Cram: Security Architecture and Models | Pearson IT Certification